Nowadays, most of our life is online or has online traces even if we don’t know it. More available personal information online gives great data to analyze for online IT businesses and large possibilities for hackers and cybercriminals.
When we travel, we are especially vulnerable, as we don’t have access to our home Wi-Fi protected by a strong password.
In this article, we will tell about possible threats to your online privacy and the best ways to protect yourself in terms of cybersecurity and privacy.
The rapid increase in the dark web network makes us apprehensive about the safety of our online identity. When we are stationed at home or office, we keep the basic tenets of online security in mind.
However, whenever we are out on tour – be it on an official trip or a vacation, we tend to let down our guard. The reasons could be many, but we run the risk of losing our identity as well as crucial documents. There could be financial losses too.
Surveys have found that travelers are well aware of the cybersecurity-related risks when traveling. Around 40% of travelers in the USA are aware that they could be targeted by cybercriminals while traveling.
And 70% of the travelers were engaging in risky activities too.
Travelers are known to do the unthinkable, including connecting to public Wi-Fi and charging their devices through a public USB station. Little do they understand the risk of their personal and financial information being stolen by cybercriminals?
In this article, we will talk about some online privacy and cybersecurity tips for travelers that will help you to always stay safe and private online.
But what exactly can happen if you are not safe online?
Cybersecurity and Online Privacy Threats
There are many ways how our personal data can be used by our governments, favorite social media, competitors, and regular hackers selling personal information in bulk.
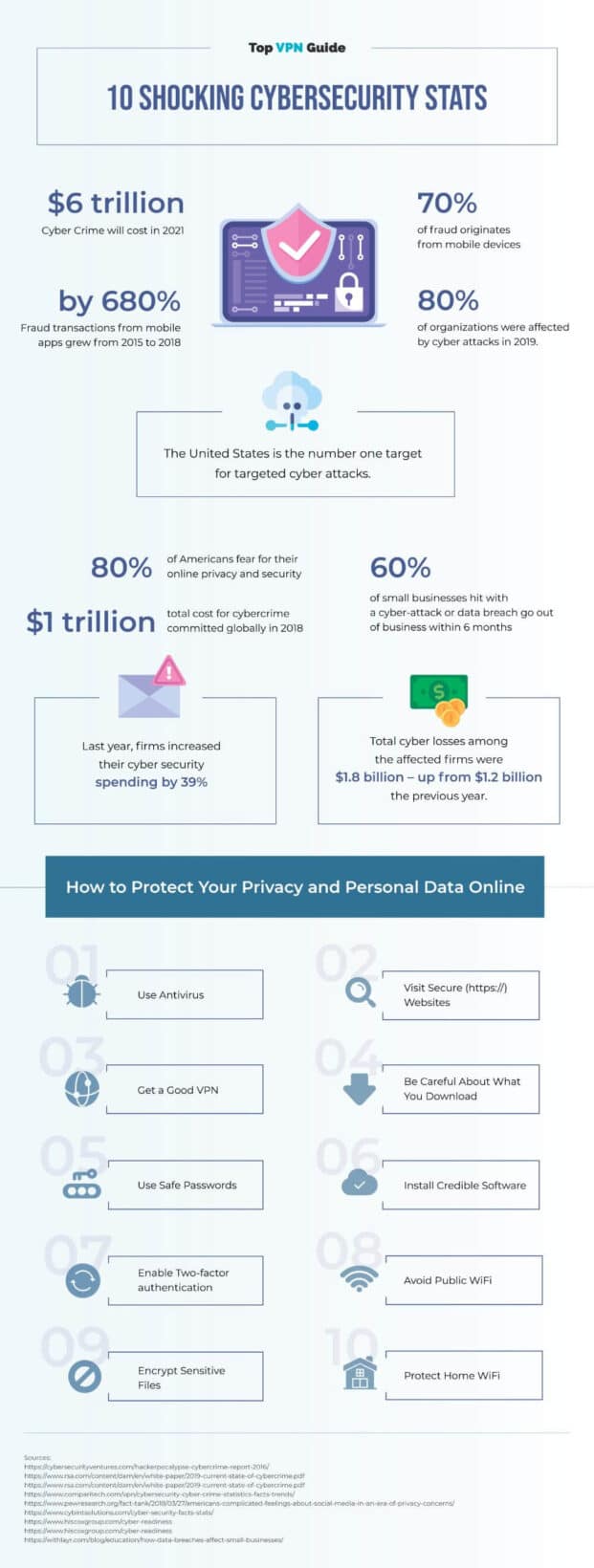
Here are some shocking cybersecurity facts you can share with your friends & family to increase their awareness of online privacy threats:
- According to a study by IBM, the average cost of a data breach in companies is $3.92M with the highest industry average being $6.45 million in Healthcare companies.
- According to TechRepublic, IT security budgets in 2019 average $18.9 million, up from 2018’s $8.9 million. Worldwide IT spending was over $3.7 trillion in 2019.
- 60% of small businesses close within 6 months of a cyberattack, according to a study of the National Cyber Security Alliance.
- 1 in 8 Businesses are destroyed by data breaches, according to the US Bank study.
But that about businesses, right? What exactly threatens me?
There are even more ways to use your vulnerable privacy or online security.
Here are some of the most common types of cyberattacks:
- DoS & DDoS – attack on server blocking access to it. It can seriously harm businesses, even though this type of cyberattacks doesn’t give direct benefits to attackers.
- Man-in-the-Middle– an attack on the connection, when the attacker tries to get between the sending and receiving parties and pretend to the system/website that he is the user.
- Phishing – sending an email pretending to be someone else trying to get personal information.
- Drive-by attack – attacker places malicious software within the code of an unsafe website that gets automatically downloaded by its visitors.
- Password attack – trying to guess the password of the user to access private information. The guesswork is mostly done by software, not manually. With weaker passwords and standard login pages for different sites, it gets especially easy.
- Eavesdropping – interception of network traffic (often in public WiFi or networks without passwords) to get passwords, credit card data, and more.
- Malware attack – worms, Trojans, and viruses often attached to another valid code or program (eg. .exe files can contain them)
But that’s real cyberattacks and hacker work.
What about Facebook? Apart from being the largest social media with the highest number of active users (2,6 Billion per month), it owns Instagram with over 1 Billion users, and 2 most popular messengers – Facebook Messenger and WhatsApp (1,3 and 2 billion users accordingly).
Mark Zuckerberg also tried buying Snapchat but because of not reaching an agreement, he simply decided to destroy it (with legal business ways).
It means that one man has access to online data of about half the world’s population!
Having this much information, it is possible to earn billions in advertising income offering advertisers (and the government) the most suitable people to target. Which Facebook did, and had multiple scandals with leaks of private data of millions of its users.
It is also under a criminal investigation for deals with electronics manufacturers to access user data.
And remember, those are just some of the apps that have access to your personal data. There are many more…
Why is an online privacy and security protection is especially important in Belarus?

As you already know, the US government is watching you. And it is not the only one.
The Belarusian government is watching people too, and it blocks websites representing different opinions than the official state media.
Some of the most popular news platforms were temporarily blocked forcing people to use VPN providers on all their devices, communicate through encrypted Telegram chats rather than VK.com, the most popular social media in the Russian-speaking internet.
You can learn more about censorship and freedom of speech in Belarus here.
Belarus has a highly-developed IT industry with world top-level specialists and 3 times higher average salaries of software engineers than a country-wide average salary (eg. a doctor).

At the same time, in terms of cybersecurity, Belarus is far behind its neighbors. According to the Global Cybersecurity Index, it is on the #69 position out of 175 countries with neighboring Lithuania on #4, Estonia on #5, even Russia being on #26, Kazakhstan #40, Moldova #53 and Ukraine on the 54th position.
Now, we had enough scaring you. 🙂
Here are the ways to stay safe and secure online while you travel (hopefully, you choose Belarus 😉
Cybersecurity & Online Privacy Tips
Knowing all that, it is clear that just a strong password and a standard antivirus are not enough to protect your privacy. You need to take several measures and maybe even change approach to sharing your data online.
Managing login proactively
Travelers must ensure that they change their login credentials for all their devices before setting out on tour. It will help them to keep their information safe by devising passwords.
The global best practices require that all passwords must contain alphabets, digits along with unique characters and must not be guessed easily, and one of the characters should be in capital letters.
They can also take the help of password managers if there are too many passwords to handle. This software can also propose the passwords, and they follow global password best practices. Handling passwords using software is crucial as it will prevent brute force attacks by cybercriminals to access your sensitive data.
Do not access insecure Wi-Fi
While traveling, you must not use public Wi-Fi connectivity. These connections are usually without any safeguards or cybersecurity protocols in place. Most of them do not even have an antivirus.
There have been incidents when people have found their systems to have been hacked after using a public Wi-Fi system. Free Wi-Fi also lures users into being victims of man-in-the-middle attacks where the user runs the risk of personal and organization data being accessed by unauthorized third parties. It is because hackers can place themselves between the traveler and connection point.
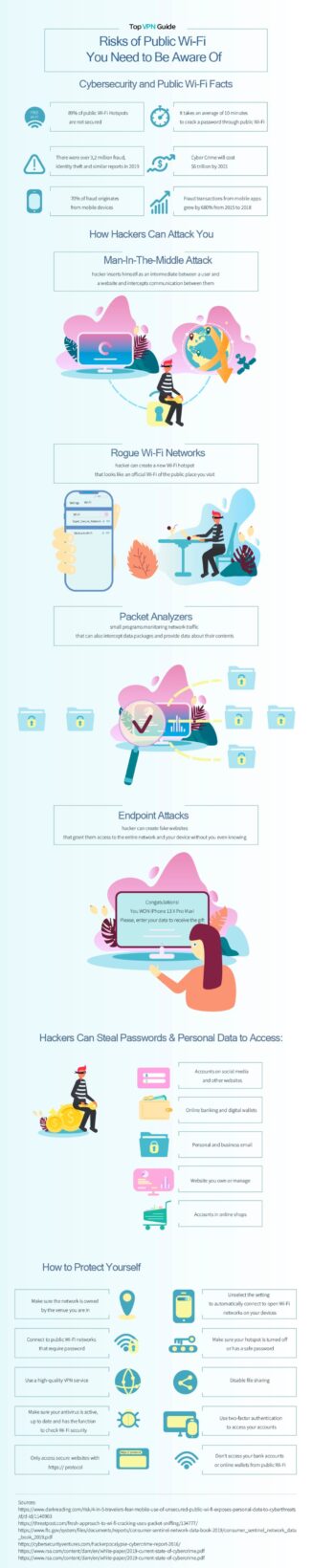
Insecure Wi-Fi systems are also subject to the distribution of malware that can wreak havoc on your confidential data. Hackers also use special kits to eavesdrop on Wi-Fi signals. Hence it is in interest to avoid using insecure Wi-Fi systems.
Always use a VPN when traveling
A VPN service helps to create a secure connection to the internet from your tablet, laptop, or smartphone. It helps to bypass geo-restrictions and allows you to work with ease.
If you are on an official trip, you must request the IT department to install a VPN that you can use for your various devices. It would help if you did not connect with any non-encrypted connections.
A VPN does not allow snoopers to gain access to confidential data on your devices. Moreover, you can prevent yourself from logging your access to various websites. You can also get anonymity while browsing online.
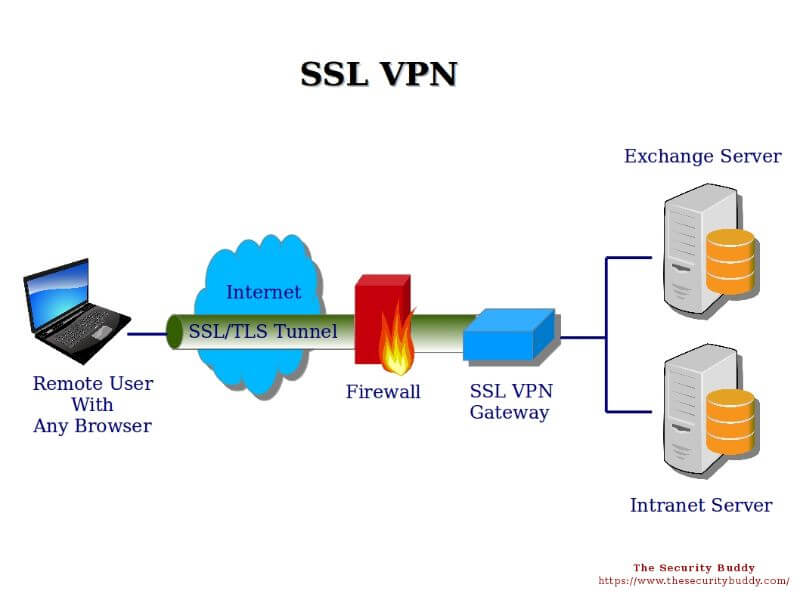
A VPN also hides your IP, and allows access blocked websites from different locations where they are not blocked (widely used in Belarus).
Check the rankings of the best VPNs for iOS, top VPN companies for Windows, and other rankings on Top VPN Guide to choose the right VPN provider for you.
Visit only HTTPS sites
Travellers must only visit HTTPS sites. It is easy to understand which sites are safe as web browsers mark unsafe non-HTTPS sites as “Not Secure.”
The HTTPS sites have an added layer of security provided by SSL certificates. The communication between the web server and the web browser is encrypted.
It will make any unauthorized access by a third-party as meaningless. While trying to make a purchase online, you must always be on your guard and check whether the site you are visiting is an HTTPS site.
You should check whether SSL certificate is from authenticated SSL providers like SSL2BUY or any reputed certificate authorities.
You must also check out for phishing scams where you may receive an email that leads you to a website similar to that of a renowned brand. Be on your guard against such emails as they use fraudulent means to gain access to your user credentials and, at times, your financial information.
Backup your data
What would you do if any hacker gained access to your data and deleted everything? It always helps to have a backup of your data at a secure location. It will help you get back the required information in the scenario of your essential data falling in the hands of hackers.
You can upload your data onto a cloud service providers like Google or Amazon AWS.
Always remember to delete the unnecessary data on your devices if you do not need them in handy. You can still download the data from the cloud location and do your work.
However, you must never forget to logout from the cloud services once you finish your task.
You must also clear the history of your work and delete it before you go out on tour. You can remove the browsing history too. If any of the histories is essential, you may upload it onto the secure cloud location.
Mobile apps can be dangerous
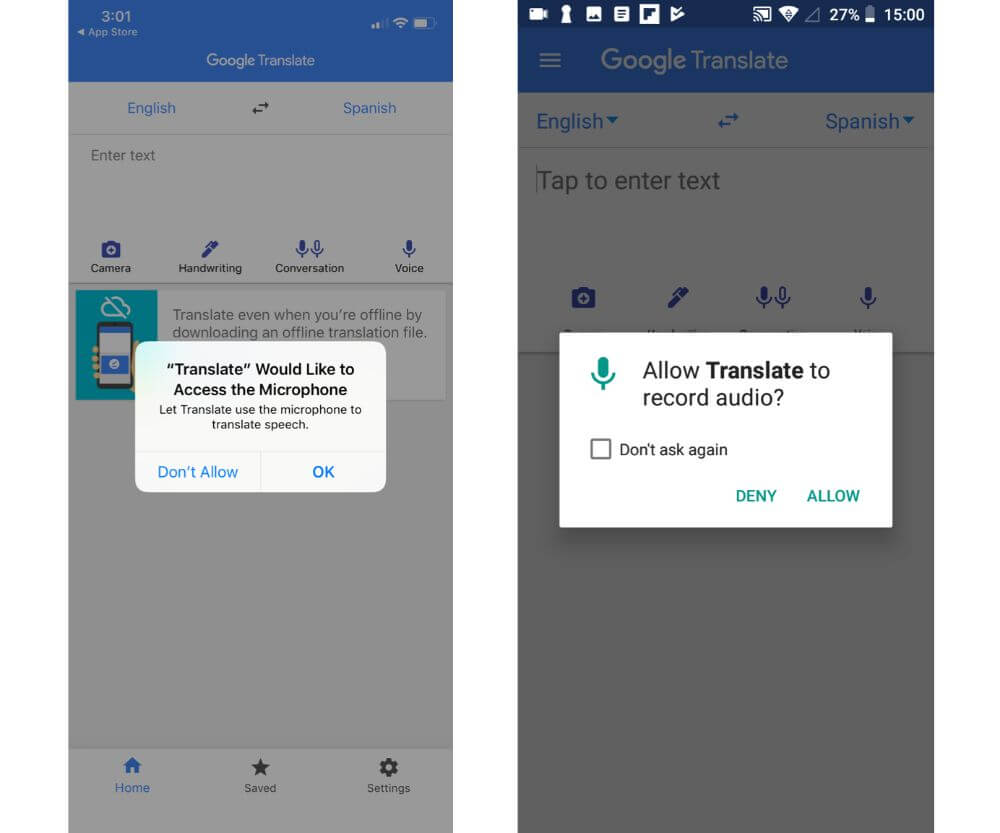
Most of us download numerous apps from the Play Store or App Store without realizing the security issues that it could bring. Most apps require access to a lot of data like location, camera, microphone, email, phone number, contacts list. And that’s by your consent (which you may not have known about
Moreover, even renowned apps get hacked, leading to the personal data of users being compromised.
It is happening despite the GDPR guidelines being in place. Due to a data breach, British Airways had been fined US$ 230 million, leading to details of 380,000 card payments being compromised. A benchmark test on favorite Android apps found that some of them were leaking sensitive information.
It always helps to keep non-essential mobile apps away from your devices. Do you need all the apps to download on your device? If not, you must delete all mobile apps that you do not need.
Lesser number of apps reduce the chances of your device being broken into, and your information falls into hackers’ hands.
Enable two-factor authentication (2FA)
Most programs and email services allow users to enable two-factor authentication. It is vital as it provides you with an additional layer of security. It is the process by which you receive a PIN on the registered mobile number.
You can log in to the system only after you enter the pin. In another scenario, the program could ask you the response to a selected question. All these processes reduce the chances of your user credentials being accessed by any third-party.
It also allows secure access to sensitive corporate information, which should not be accessed by unauthorized personnel. The 2FA procedure also helps you to reset your password easily. While buying anything online, always look out for sites that allow 2FA as it builds secure relationships.
Be cautious from external devices

Very often, we allow our colleagues to use our devices to share confidential data. While it could be the unofficial norm in the workplace, it is a dangerous activity when you are on tour. You must not allow any unknown person to plug in any external device to your laptop or handheld device.
One of the significant sources of viruses is through flash drives and external hard disks. Ideally, it would be best if you disable your laptop’s ports before going out on tour. Always avoid sending documents using the document sharing software and cloud systems. If the document is too large, zip it and send out or break it into parts.
Keep your antivirus updated
Before setting out on tour, you must keep the software on your devices updated. The antivirus on your laptop must be updated to the latest version.
Most antiviruses are updated regularly with newer viruses and malware. The updates help to plug any security loopholes that may have been there in the earlier version.
It is not easy to know when the updates would be available. For this reason, you must always turn on the notification to receive alerts on any product upgrade. Always ensure you use the best antiviruses in the market that also bundles a firewall. It helps to safeguard against any cyber-attack.
Conclusion
Travelers rarely pay heed to cybersecurity protocols when they are out on tour. But when they are traveling, the chances of being a victim of a data breach are more. You can be safe by using a VPN to connect to the internet.
In this article, we have discussed various tips for travelers to stay safe from cyber-attacks. Businesses must undertake regular training and workshops for their employees on these aspects. The list must not seem overwhelming, and people usually get used to these security measures.